Tooling · hackpass · 2026-05-14
Introducing HackPass - Deliberately Vulnerable Password Manager (Windows/macOS)

Contents
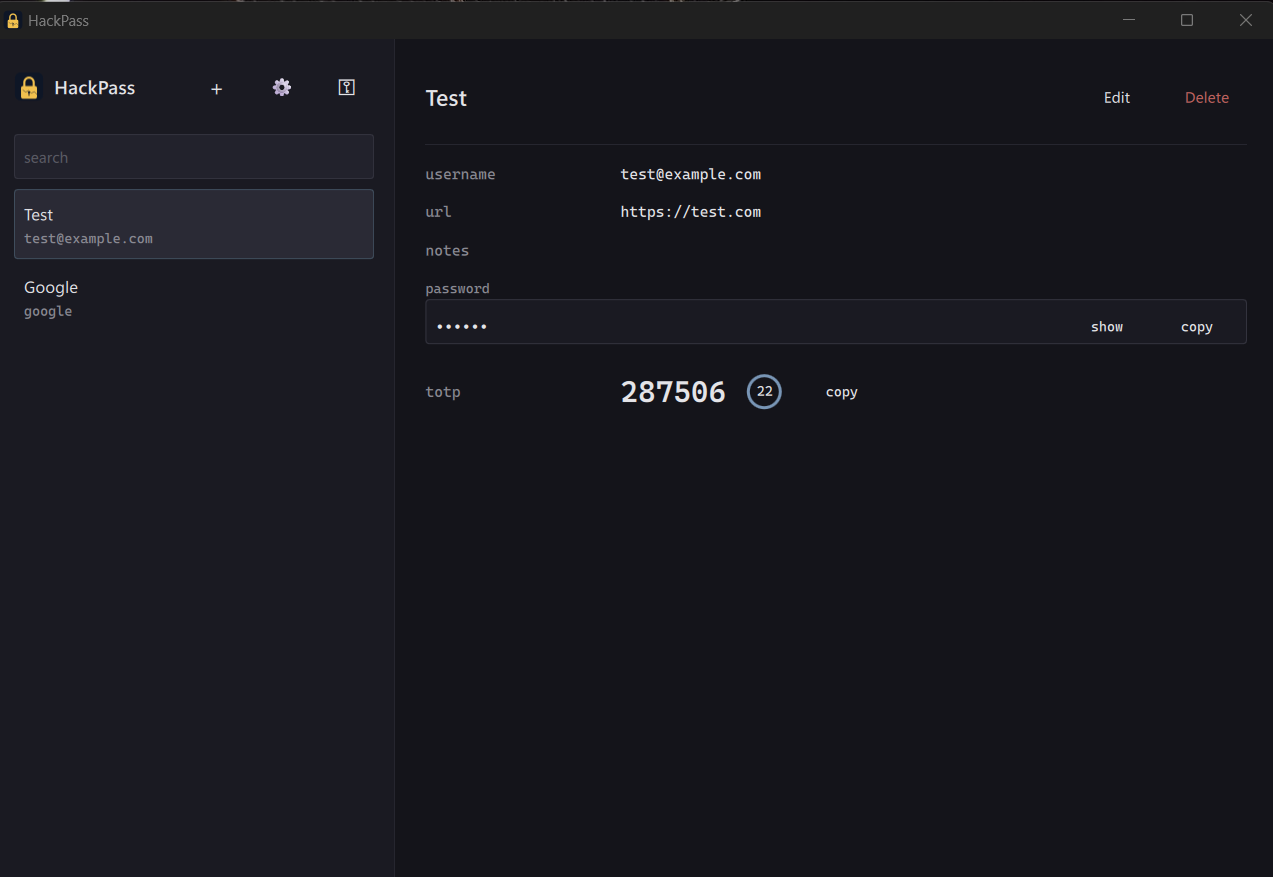
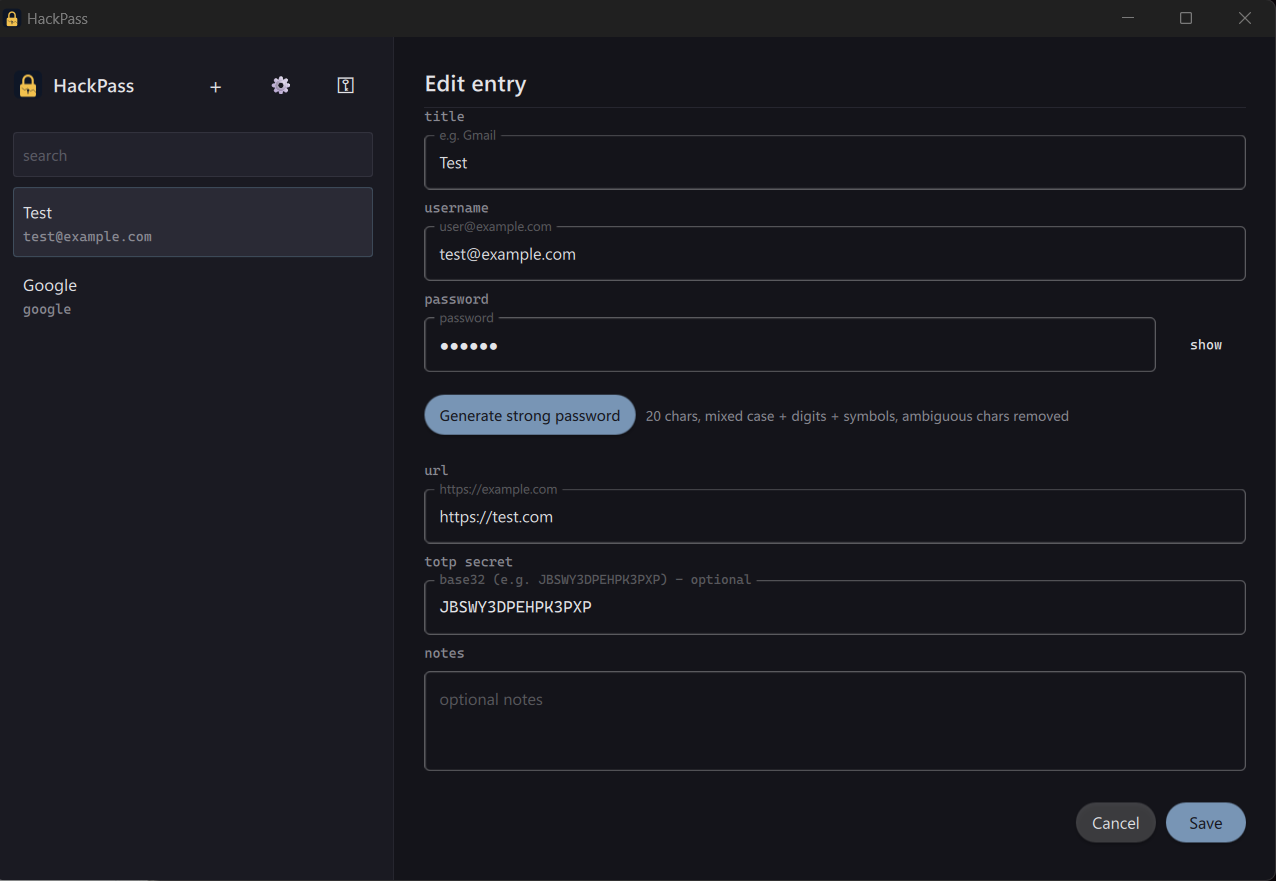
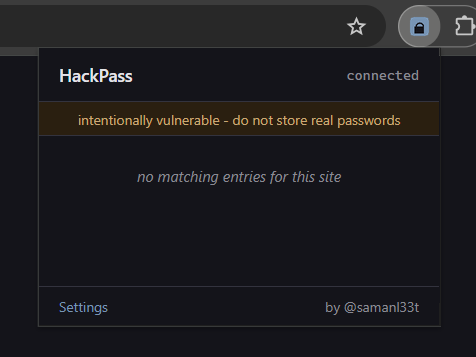
HackPass v1.0.0 is out: github.com/samanL33T/HackPass. I’ve been building this on and off for a few weeks, and it’s reached the point where it’s worth handing to other people and LLMs to break. It’s a deliberately vulnerable password manager specifically to practice analysing Qt6-based desktop applications. It’s not a real password manager. It’s a target for runtime instrumentation and reverse engineering. Don’t put real credentials in it.
Features
- Vault with search, edit, and TOTP support
- Master-password unlock through a KDF
- Chrome MV3 browser extension for autofill, talking to the app over a localhost WebSocket
- Self-hosted TypeScript backend on Bun for sync, license, policy, and server-pushed messages
- TLS with TOFU pinning between app and backend
- License gating for “premium” features (export, sync, plaintext dump)
- Hardening toggles in Settings: anti-debug, integrity checks, screenshot blocker
- First-run wizard, sample vault, and switch script for flipping server-side policy on demand
Vulnerabilities
Complete list of vulnerabilities can be found in the README. A few of the more interesting ones:
- Hookable plaintext boundaries in the crypto layer
- Custom obfuscation passed off as encryption
- Partial-length token comparison in authentication
- Confused-deputy attack surface across the QML to C++ bridge
- Centralised anti-debug hardening with a single point of failure
- Server-controlled destructive operations on the client
- etc.